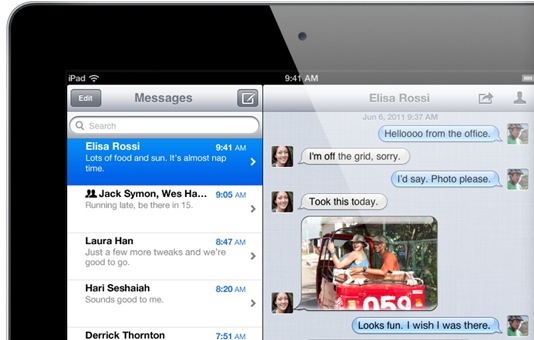
It hasn’t been a good few months for Apple and their security department. For a company that is usually well-known for their security, Apple has experienced a few high-profile vulnerabilities, from the Evasi0n Jailbreak, to the lockscreen bypass bug, and now an iMessage security flaw that could leave any user susceptible to a Denial of Service attack.
Many Apple developers have already reportedly been targeted by the iMessage security flaw, including notorious Jailbreak developers such as iH8Sn0w and chpwn, with the origin of the attacks unknown.
The attacks were setup by individuals or a group of individuals using an AppleScript and fake email accounts, making tracking and prevention alot more difficult.
Grant Paul (@chpwn) on Twitter states:
“The iMessage spammer has now completely locked me out of my iOS Messages app … by sending long strings of Unicode chars.”
iMessage Security Flaw
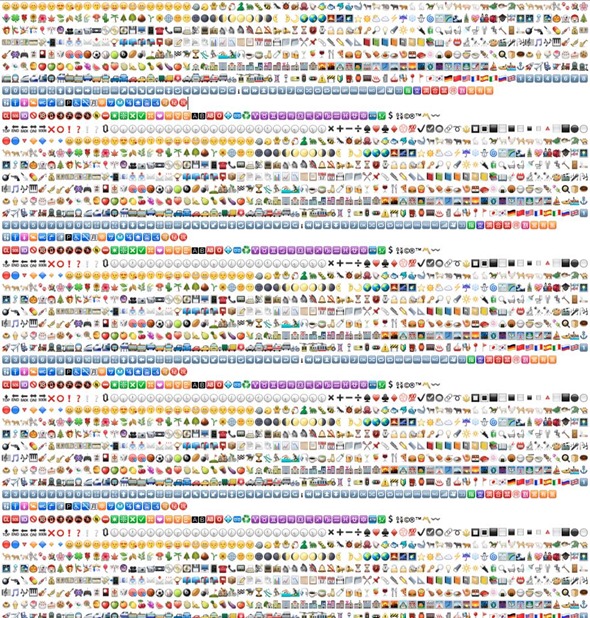
Sending multiple messages quickly, or long strings of Emoji unicode characters, to someone repeatedly will cause their iMessage app to crash and eventually their account to be locked out. The image below gives you an idea of the message length necessary to cause such an issue.
The iMessage Security Flaw will be to do firstly with the back-end infrastructure rendering of the unicode messages, as well as Apple’s backoff mechanism for preventing spamming. The issue is, they seem to be blocking the receiver of the spam, rather than the spammer themselves.
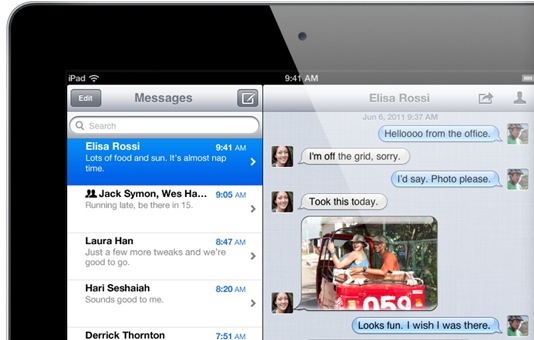
While the iMessage Security Flaw remains open, and up until now only small-scale attacks have been launched, the threat ever remains of something more large-scale.
Apple are yet to comment on the issue.
It is not recommended you try this on any of your contacts, as it is unknown what Apple will do to those accounts that are found to be abusing the service. If you find yourself getting spammed, immediately proceed into Settings.app to turn off the iMessage service to avoid any issues.